The world of hackers is one that has evolved dramatically over the past few decades. From the early days of phone phreaking to the current era of modern cybersecurity and CTF (Capture The Flag) or bug bounty programs, the world of hacking has seen its fair share of changes. In the 1960s and 70s, phone […]
Security has always been a top concern for individuals, organizations, and governments. Historically, manned guarding has been the primary method of securing a location or asset. Trained security personnel would patrol the premises, monitor surveillance systems, and respond to any potential threats. While this method has proven to be effective, it has its limitations. With […]
In the world of virtual reality, security is just as important as in the real world. That’s why our in-house cyber team, Red Team Consultants, has been working tirelessly to ensure the safety and security of our platform, Chase Reality Metaverse. Recently, we discovered an impersonation scam that was targeting our members, with the culprits […]
Welcome to the world of tomorrow, where technology has surpassed our wildest imaginations. The rise of artificial intelligence (AI) has brought about a new era of possibilities and advancements that are changing the way we live, work, and communicate. From smart homes to self-driving cars, AI is revolutionizing our daily lives, and nowhere is this […]
RFID cloning is a type of identity theft that involves copying the data stored on a RFID (Radio-Frequency Identification) chip, which is commonly found in things like passports, credit cards, and key cards. This allows the attacker to create a duplicate card or device that can be used to gain access to restricted areas or […]
Have you ever heard of the deep web or the dark web and wondered what they are and how they differ from the regular internet we use every day? The deep web and the dark web are often misunderstood or conflated, but they are actually quite different. In this blog, we’ll take a closer look […]
When it comes to choosing an operating system for ethical hacking and penetration testing, two of the most popular choices are Parrot OS and Kali Linux. Both of these Linux distributions are designed with cybersecurity professionals in mind, but they have their own unique features and capabilities. In this blog, we will compare Parrot […]
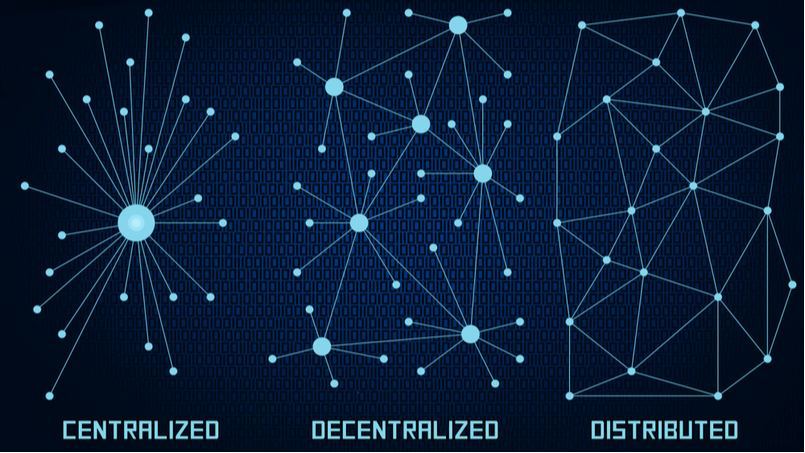
As the internet continues to evolve and expand, it’s become increasingly clear that traditional centralized systems are not equipped to handle the growing demands and challenges of the digital age. From data breaches and censorship to central points of failure and control, the limitations of the current internet infrastructure have become more apparent than ever. […]
CCTV (closed-circuit television) systems are a common security measure used by businesses and organizations to monitor and protect their premises. While CCTV systems can be a valuable tool for deterring crime and providing evidence in the event of an incident, it is important to ensure that they are properly secured to protect against unauthorized […]
Are you a hacker of cyber security tester looking to expand your skillset and learn about the ins and outs of Bluetooth device exploitation? Look no further! This blog will provide a thorough overview of the tools and techniques used to hack Bluetooth devices. First, let’s start with the basics. What is Bluetooth, and […]