Well there are many attack vectors that cyber criminals can use to acquire access to systems and personal information most of them can be placed into only a few method types. 1. Direct access from brute force attack or DDOS ect (this is when an attacker finds information about your business or personal information online […]
We are talking about PCI compliance. What is PCI compliance and why is it so important to your business? Payment card industry (PCI) compliance is mandated by credit card companies to help ensure the security of credit card transactions in the payments industry. Payment card industry compliance refers to the technical and operational standards that […]
Lets Cast a Net on your Internet security, The Red Blog Internet security is something that we all need, especially when more of our daily lives rely on the use of computers and other smart devices. With the growing risk from hackers and Internet scammers. Viruses, malware and other cyber crime. Knowing the basics of […]
The Red Blog, Open Wallets, Worthless Virtual Land and so much more! The shift of trust with our personal data has taken a dark twist recently, with tech companies and big pharmaceutical under the spotlight. From virtual gang rape on the Facebook Meta VR platform, where multiple avatars attacked Nina Jane Patel, to the already […]
Red Blog Cyber With the rise of A.I technology and the Internet of things or IOT everything becomes linked to the Internet and therefore a risk from hackers. From automated Self driving cars being taken over and crashing into Walls. To home security systems being hacked, Even your own fridge linked to your bank account. […]
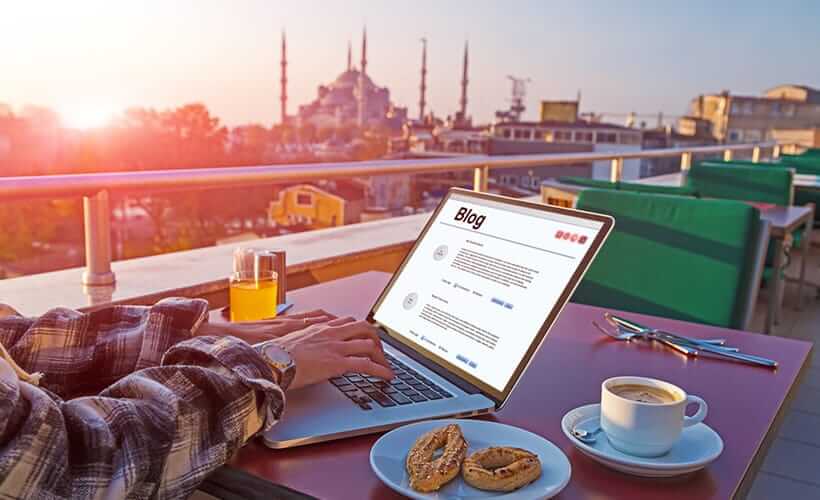
Security in uncharted locations as a digital nomad
Red Blog Cyber, What is blockchain security? Blockchain security is a comprehensive risk management system for a blockchain network, using cybersecurity frameworks, assurance services and best practices to reduce risks against attacks and fraud. Quote taken from the IBM website on cyber security and blockchain. Red Team Physical and Forced Entry Consultants have been working […]
Red Blog Cyber Reliable secure and cheap I.T projects are as easy as PI We are talking about the Raspberry Pi.A computer the size of a smartphone.But how do they compare to home computers? The average RAM on Raspberry Pi is about 1 GB, with a maximum of 8 GB on the Raspberry Pi 4. […]
Red Blog Cyber Setting up to leave the back door open. Following on with our previous blog (so you want to be a hacker) So you want to be a hacker? Now it’s time to create a profile on your target in order to create an explot to compromise their systems. This stage could be […]
Who’s watching the watchers? Personal and physical identity are both at risk from criminals as well as companies that we trust. From identity theft to the selling of Personal data every time we are going about our lives someone is trying to gather information about us, this could be for criminal purposes such as stealing […]